Hacking a valid cert into the EAP controller software
Hacking a valid cert into the EAP controller software
So let's start by saying I hate invalid certificate errors. I've worn many hats: DevOps, IT Support, Customer Support, Web Designer, and more; each and every one screams "FIX IT" when I see one of these errors. Naturally, when I got my new access points (yes I use my EAP245 for my home), I was dismayed to see the invalid certificate error on the management page.
Well I have my own domain name that I use for my home network devices and have used it to put valid certs on them (a pfSense router, an OMV file server, and a couple other gadgets), and thought to myself, "why can't I have a valid certificate on the EAP controller?"
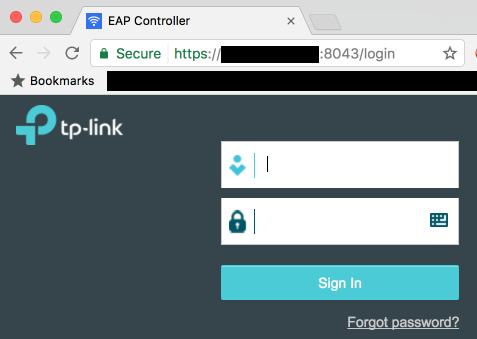
After many hours of poking around with much trial and error, I successfully managed to get the green padlock indicating a valid certificate!
DISCLAIMER: Proceed at your own risk! This worked for me, but I cannot guarantee that this process will not bork your EAP controller, invalidate your warranty, and/or kick an orphaned puppy. Please, think of the puppies.
PREREQUISITES
[*]A domain name that you control DNS for
[*]A way to run the openssl command (either via a handy Linux/Mac box laying around, or an OpenSSL package for Windows on your controller or a handy Windows box)
[*]Full access to your EAP controller box
[*]Depending on your cert provider, an HTTP host you can use for verification
PREPARING
[*]Create a subdomain for your controller under your desired domain name, e.g. "eap.example.com"
[*]If your cert provider requires HTTP verification (e.g. LetsEncrypt), start by pointing this at an HTTP host you have access to, with a very low TTL
PROCESS
[*]Shut down the EAP Controller software
[*]Make a copy of your current keystore (EAP Controller\keystore\eap.keystore) for safekeeping
[*]Generate a private key and CSR:
openssl req -out MYSITE.csr -new -newkey rsa:4096 -nodes -keyout MYSITE.key
[*]Submit your CSR and get the cert from the CA
[*]If your CA uses HTTP verification, once the process is complete change your DNS entry to point to your EAP controller's IP address
[*]Combine your cert and private key into a PKCS#12 key:
openssl pkcs12 -export -in MYSITE.crt -inkey MYSITE.key -name eap -out MYSITE.p12
it is important that the "name" parameter is "eap"!
[*]use an easy-to-remember password, you'll need it a few steps later (then it will be irrelevant)
[*]Make a copy of your current keystore (EAP Controller\keystore\eap.keystore) for safekeeping (you already did that right?)
[*]Delete the eap.keystore file in EAP Controller\keystore
[*]Import your PKCS#12 key into a new keystore:
keytool -importkeystore -deststorepass tplink -destkeystore eap.keystore -srckeystore MYSITE.p12 -srcstoretype PKCS12
enter the password you specified in step 5 when prompted
[*]Restart the EAP Controller software!
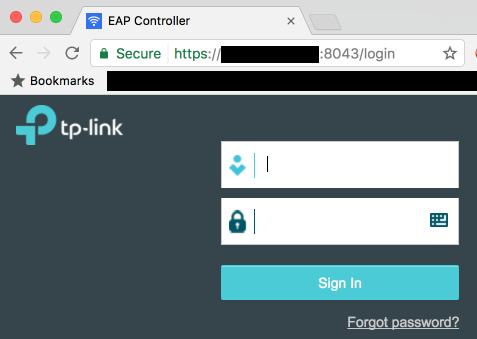
When it starts and loads the page, you should still see a certificate error; this is because it loads to https://127.0.0.1 which is never a valid hostname. If you browse to the hostname you created, e.g. https://eap.example.com:8043/ (don't forget the port number) you should now see the valid certificate!
Well I have my own domain name that I use for my home network devices and have used it to put valid certs on them (a pfSense router, an OMV file server, and a couple other gadgets), and thought to myself, "why can't I have a valid certificate on the EAP controller?"
After many hours of poking around with much trial and error, I successfully managed to get the green padlock indicating a valid certificate!
DISCLAIMER: Proceed at your own risk! This worked for me, but I cannot guarantee that this process will not bork your EAP controller, invalidate your warranty, and/or kick an orphaned puppy. Please, think of the puppies.
PREREQUISITES
[*]A domain name that you control DNS for
[*]A way to run the openssl command (either via a handy Linux/Mac box laying around, or an OpenSSL package for Windows on your controller or a handy Windows box)
[*]Full access to your EAP controller box
[*]Depending on your cert provider, an HTTP host you can use for verification
PREPARING
[*]Create a subdomain for your controller under your desired domain name, e.g. "eap.example.com"
[*]If your cert provider requires HTTP verification (e.g. LetsEncrypt), start by pointing this at an HTTP host you have access to, with a very low TTL
PROCESS
[*]Shut down the EAP Controller software
[*]Make a copy of your current keystore (EAP Controller\keystore\eap.keystore) for safekeeping
[*]Generate a private key and CSR:
openssl req -out MYSITE.csr -new -newkey rsa:4096 -nodes -keyout MYSITE.key
[*]Submit your CSR and get the cert from the CA
[*]If your CA uses HTTP verification, once the process is complete change your DNS entry to point to your EAP controller's IP address
[*]Combine your cert and private key into a PKCS#12 key:
openssl pkcs12 -export -in MYSITE.crt -inkey MYSITE.key -name eap -out MYSITE.p12
it is important that the "name" parameter is "eap"!
[*]use an easy-to-remember password, you'll need it a few steps later (then it will be irrelevant)
[*]Make a copy of your current keystore (EAP Controller\keystore\eap.keystore) for safekeeping (you already did that right?)
[*]Delete the eap.keystore file in EAP Controller\keystore
[*]Import your PKCS#12 key into a new keystore:
keytool -importkeystore -deststorepass tplink -destkeystore eap.keystore -srckeystore MYSITE.p12 -srcstoretype PKCS12
enter the password you specified in step 5 when prompted
[*]Restart the EAP Controller software!
When it starts and loads the page, you should still see a certificate error; this is because it loads to https://127.0.0.1 which is never a valid hostname. If you browse to the hostname you created, e.g. https://eap.example.com:8043/ (don't forget the port number) you should now see the valid certificate!

